SIM-Based Identity Authentication. Secure Messaging. One Platform.
No app. No OTP. No phone number dependency.
Trusted by innovators in 180+ countries.
Our Valued Partner Network
Key Features
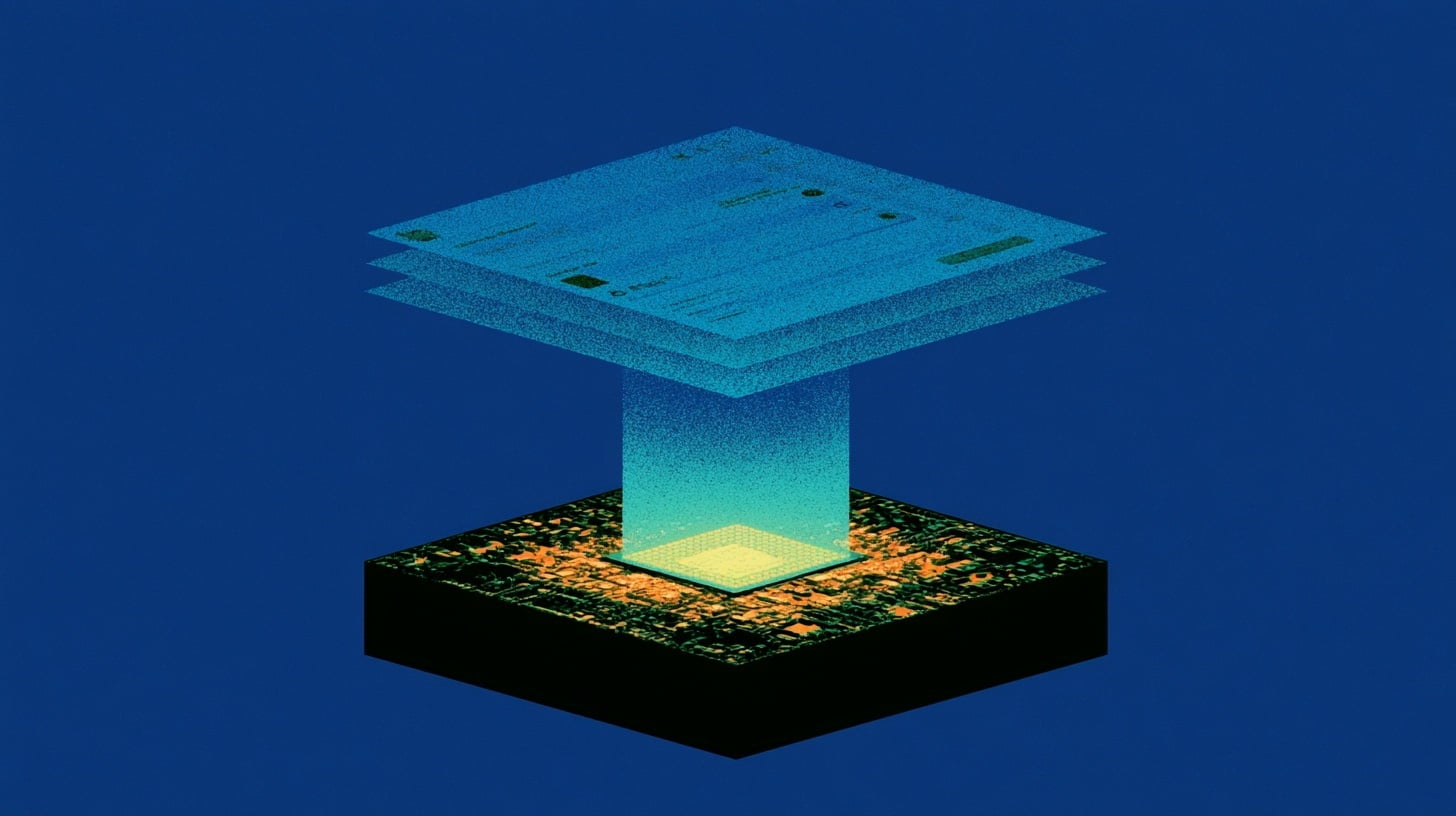
Hardware-Rooted Trust Through a Dedicated Channel
SLC authenticates through the SIM/eSIM and mobile network, creating a dedicated channel resistant to spoofing, SIM swaps, and phishing—even on compromised devices.
Seamless Experience
No app to install, with the option to use frictionless silent authentication or SIM-based user approval for sensitive actions.
Built for Global Scale
Integrated with 600+ mobile networks across 180+ countries. One API unlocks worldwide reach—including eSIM.
Out-of-Band by Design
Authentication flows through a dedicated channel independent of device, number, or operating system—a channel that cannot be accessed through the public internet.
Simple API Integration
Plug SLC into your existing workflows using lightweight REST or GraphQL APIs. Fast to deploy, easy to test.
Future-Proof Architecture
Continuously evolving to stay ahead of emerging threats—including AI-driven fraud, deepfakes, and increasingly sophisticated attack techniques.
If the Real, Authorized Device Isn't Present, the Action Doesn't Happen
SLC authenticates through the SIM/eSIM and mobile network, establishing hardware-rooted, cryptographic proof that the real, authorized device is present and trusted. This dedicated channel cannot be accessed through the public internet, intercepted via phone number, or replicated by any app. Only the real device can respond.
A Dedicated Channel for Critical Conversations
SLC's secure messenger deploys a secondary eSIM to create a dedicated, phone-numberless communication channel—completely independent of the user's primary number. This channel cannot be accessed through the public internet, making it invulnerable to phishing and social engineering. Mutual authentication between customer and organization ensures only verified parties can communicate.

Why Enterprises
Choose SLC
SLC strengthens existing security stacks with a foundational trust layer—helping enterprises protect high-impact actions, reduce fraud risk, and build customer confidence.
Enhance Security
Authenticate through a dedicated channel between your enterprise and the customer's device. Because trust is rooted in hardware, it cannot be phished, forwarded, or socially engineered.
Ensure Continuous Compliance
Meet regulatory requirements with continuous identity assurance. Hardware-rooted, cryptographic proof of identity and intent supports compliance across regulated industries.
Streamline Onboarding
Accelerate customer acquisition with frictionless authentication. No app to install, no OTPs to enter—just secure, hardware-rooted authentication that works in the background.
Reduce Operational Costs
Automate complex authentication processes and minimize manual interventions, significantly lowering operational expenses while improving accuracy.
Boost Customer Trust
Build confidence by protecting high-impact actions—financial transactions, privileged access, and critical approvals—through the most secure communication channel available.
Future-Proof Your Operations
Stay ahead of emerging threats with a platform continuously evolving to counter AI-driven fraud, deepfakes, and increasingly sophisticated attack techniques.
Recognised among the world's leading FinCrime innovators.

The Latest Insights
Explore a curated collection of guides, tools, and insights designed to help you get the most out of our products and services.